Tom is considering replacing his standard antivirus protection with "application control." With all of the choices, he would like to find a program that offers the same features he has come to rely on with TeamsID.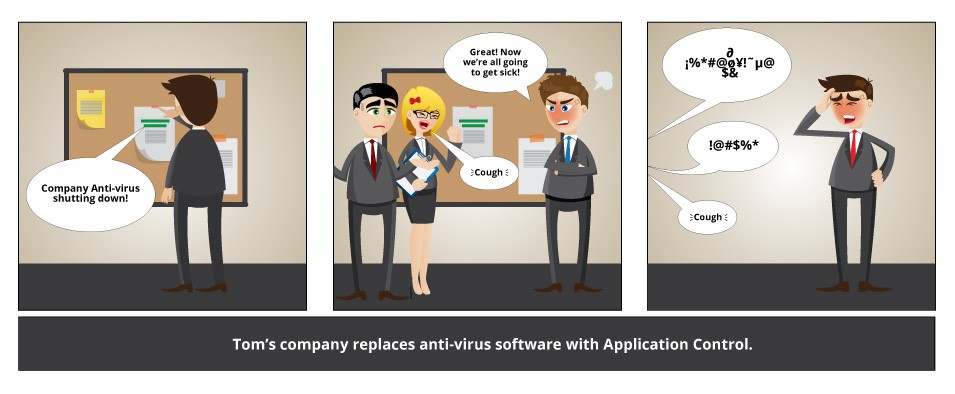
Tom wants a program that is easy to use.
Tom knows that the best program is one that does its job efficiently and reliably. He needs a program that is there when he needs it and keeps things secure when he's on the go. Another feature would be collaborative capabilities. When he can't manage the program, Tom would love a program that he could share accessibility with the people he trusts.
Tom wants a program that is mobile.
Tom has grown accustomed to having access to company records from anywhere at anytime. By using TeamsID, he never has to worry about accessing records using different devices. Tom would like to find an application control program that provides a software that is easy to install on multiple devices while not compromising security.
Tom wants a program that is affordable.
Like TeamsID, Tom wants to find a program that provides exceptional service at an affordable cost. "You will come across all kinds of versions and features priced across a broad scale," wrote John Chadder for Business 2 Community. "Some software is free while others cost hundreds of dollars. You want to go with something reasonable; it is not necessary to buy the most expensive program to keep your computer secure."
Like TeamsID, the best feature of all would be the peace of mind in knowing his application control software is easy to use, mobile, and affordable. He feels safe already.
Read more about Tom's Password Secrets, and how common password mistakes and simple tricks and tools to build a secure perimeter around your data--and your organization's. Click here to download it now.