SplashData’s fifth annual “Worst Passwords List” shows people continue putting themselves at risk
While longer passwords debut on this year’s list of most commonly used passwords, they are not necessarily more secure
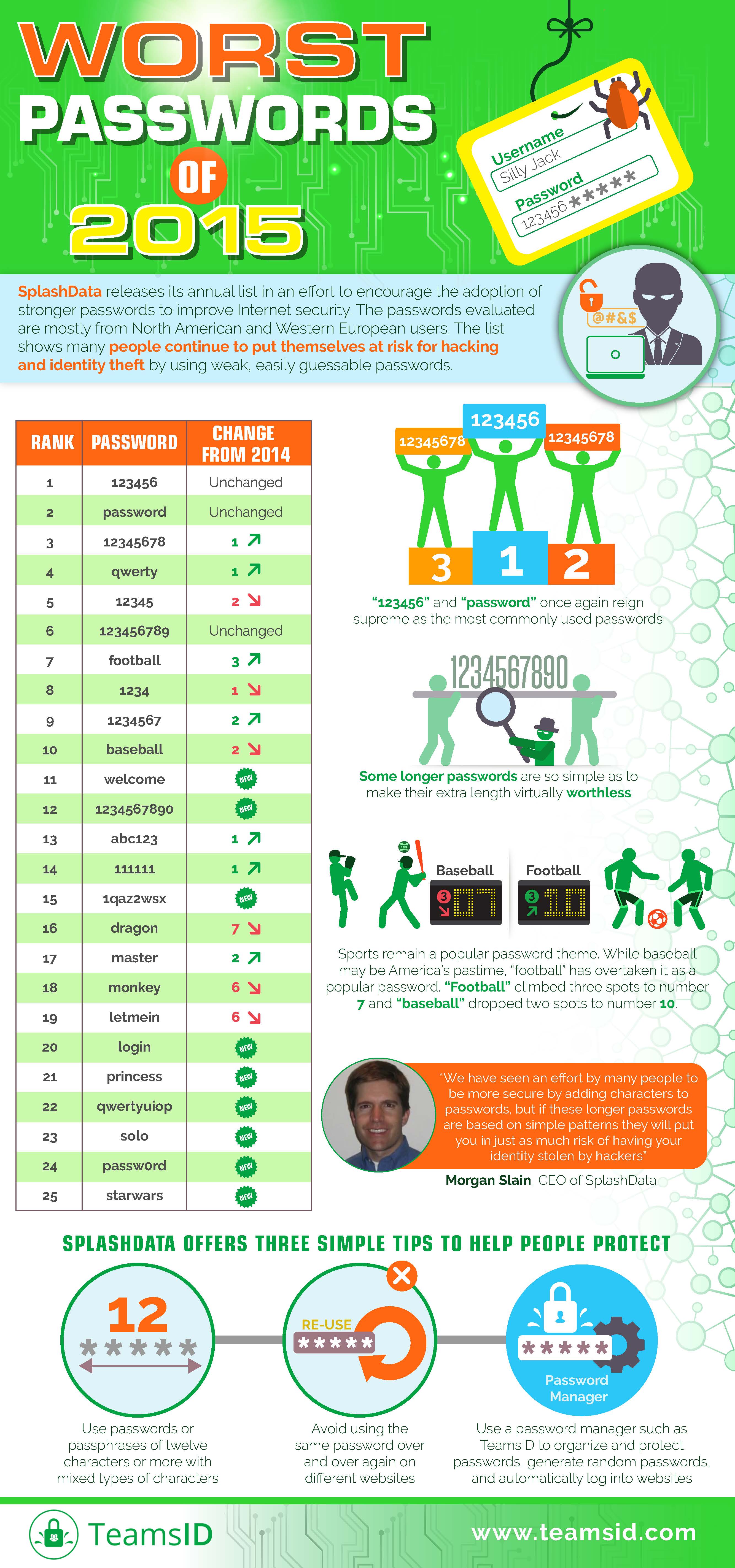
LOS GATOS, CA – SplashData has announced the 2015 edition of its annual “Worst Passwords List” highlighting the insecure password habits of Internet users. “123456” and “password” once again reign supreme as the most commonly used passwords, as they have since SplashData’s first list in 2011, demonstrating how people’s choices for passwords remain consistently risky.
In SplashData’s fifth annual report, compiled from more than 2 million leaked passwords during the year, some new and longer passwords made their debut – perhaps showing an effort by both websites and web users to be more secure. However, the longer passwords are so simple as to make their extra length virtually worthless as a security measure.
Click here to download as a pdf
For example, “1234567890”, “1qaz2wsx” (first two columns of main keys on a standard keyboard), and “qwertyuiop” (top row of keys on a standard keyboard) all appear in the top 25 list for the first time, but they are each based on simple patterns that would be easily guessable by hackers.
As in past years’ lists, simple numerical passwords remain common, with six of the top 10 passwords on the 2015 list comprised of numbers only.
Sports remain a popular password theme. While baseball may be America’s pastime, “football” has overtaken it as a popular password. Both appear in the Top 10 of SplashData’s list, with “football” climbing three spots to number seven and “baseball” dropping two spots to number 10.
When it comes to movies and pop culture, The Force may be able to protect the Jedi, but it won’t secure users who choose popular Star Wars terms such as “starwars,” “solo,” and “princess” as their passwords. All three terms are new entries on this year’s list.
Click here to download our eBook Worst Passwords: What We Have Learned From Five Years of Studying the Internet’s Most Commonly Used Passwords
Other passwords appearing on the 2015 list that did not appear on the 2014 list include “welcome”, “login” and “passw0rd.”
SplashData, provider of password management applications including SplashID for consumers and TeamsID for businesses, releases its annual list in an effort to encourage the adoption of stronger passwords to improve Internet security. According to SplashData, the passwords evaluated for the 2015 list were mostly held by users in North America and Western Europe. The “Worst Passwords List” shows that many people continue to put themselves at risk for hacking and identity theft by using weak, easily guessable passwords.
“We have seen an effort by many people to be more secure by adding characters to passwords, but if these longer passwords are based on simple patterns they will put you in just as much risk of having your identity stolen by hackers,” said Morgan Slain, CEO of SplashData. “As we see on the list, using common sports and pop culture terms is also a bad idea. We hope that with more publicity about how risky it is to use weak passwords, more people will take steps to strengthen their passwords and, most importantly, use different passwords for different websites.”
Presenting SplashData’s “Worst Passwords of 2015”:
| Rank | Password | Change from 2014 |
| 1 | 123456 | Unchanged |
| 2 | password | Unchanged |
| 3 | 12345678 | Up 1 |
| 4 | qwerty | Up 1 |
| 5 | 12345 | Down 2 |
| 6 | 123456789 | Unchanged |
| 7 | football | Up 3 |
| 8 | 1234 | Down 1 |
| 9 | 1234567 | Up 2 |
| 10 | baseball | Down 2 |
| 11 | welcome | New |
| 12 | 1234567890 | New |
| 13 | abc123 | Up 1 |
| 14 | 111111 | Up 1 |
| 15 | 1qaz2wsx | New |
| 16 | dragon | Down 7 |
| 17 | master | Up 2 |
| 18 | monkey | Down 6 |
| 19 | letmein | Down 6 |
| 20 | login | New |
| 21 | princess | New |
| 22 | qwertyuiop | New |
| 23 | solo | New |
| 24 | passw0rd | New |
| 25 | starwars | New |
SplashData offers three simple tips to help people protect themselves:
- Use passwords or passphrases of twelve characters or more with mixed types of characters
- Avoid using the same password over and over again on different websites
- Use a password manager such as SplashID to organize and protect passwords, generate random passwords, and automatically log into websites
For more information on SplashData’s last five years of research into commonly used passwords, please visit: http://content.teamsid.com/worst-passwords-ebook
# # #
About SplashData:
SplashData has been a leading provider of password management applications for over 15 years. The company’s SplashID (www.splashid.com) consumer application has grown to be one of the most trusted multi-platform password solutions with over 1 million users worldwide. SplashID’s popularity continues to rise as the number of user names, passwords, and account numbers most people have to remember is rapidly multiplying. At the same time, the risk of this kind of sensitive information falling into the wrong hands has never been greater. SplashID helps solve this dilemma by creating an encrypted digital safe available on smartphones, computers, USB keys, or online, offering the peace of mind of being able to access critical information whenever needed while maintaining the security of 256-bit encryption. The company’s business password manager TeamsID (www.teamsid.com) enables organizations to manage and share passwords and other sensitive records easily and securely. SplashData was founded in 2000 and is based in Los Gatos, CA.
PRESS CONTACT:
Kevin Doel
TalonPR, Inc.
785-554-5336
[email protected]
621 Comments on "Announcing Our Worst Passwords of 2015"
Fred Bisternet
January 19, 2016How about never, ever use a word. Dictionary hacking
Morgan
January 19, 2016Good advice!
eff
January 19, 2016Full sentences with capitalization and punctuation? https://xkcd.com/936/
Morgan
January 19, 2016Love XKCD!
Ethan
February 19, 2017easy way to remember password is choose a song lyric or quote and take tth fiirst letter of each word and add symbols.
Example:
Sometimes the right path is not the easiest one
*Strp!nte0$195-3
So hard to guess and change them every 75-90 days
Rasmus
January 20, 2016Bad advice. Use words. Note the -s. And mix words from other languages than your main ones.
Example:
The 1st boy on the streetabc. [2.2 × 10^55 possible combinations] (abc added to match number of characters)
The 1st garçon on the straße. [1.11 × 10^65 possible combinations]
Netizen Joe
January 19, 2016What's the sample size for this data? And isn't the bigger security breach that you're looking at people's passwords and reporting publicly on it?
Morgan
January 20, 2016For 2015, our report was based on over 2 million passwords we found from searches of publicly released "plain text" password posts or "dumps" on the Internet. The goal of the annual report is to encourage people to make stronger passwords. We are simply reporting findings based on information that has already been publicly posted; we are not associating these passwords with any specific user accounts.
Wii
January 20, 2016Joe, you have any rebuttal to Morgan's explanation?
FRANK
January 22, 2016I'd say it's easier to teach a few devs to deploy security measures like requiring complex passwords, locking users at failed attempts and storing them in a proper manner (hash, salt, etc) than to teach every single user about using weak passwords
Steve
January 19, 2016People who break into other people's Facebooks, emails, etc need to get a life ......they are total losers without a purpose.
watchdogman
January 20, 2016Hackers, Identity thieves and those that create viruses should all be put into prison for 50 years, or if much damage done they should be executed!
z
January 20, 2016nope, users should just protect their passwords more, its their account, their responsibility.
Gary
January 21, 2016That is a very poor and misguided response - it is the hacker who is responsible for illegally breaking into another persons property.
Just because they have not secured something like this to the nth degree, does not mean that the hackers are not criminals. In Australia, we have council pick-ups, and we leave the recycling out on the footpath. If anyone else , except the council picks it up anything, legally it is stealing and can be arrested and convicted (it is still the homeowners property until the council picks it up). Same goes if they steal your locked car out of your garage - this is similar to hacking into their accounts.
These people are highly disruptive to society and are criminals. Sure we can inform people on ways to better secure their accounts, just like we can inform people about security alarms, et cetera for cars. It does not matter how well secured a car is, a determined thief will find ways to steal the car, and the same applies for computers. To steal any car, no matter how well secured, even if it is left unlocked and they just take something from the car, it is still a criminal offence.
Although I do fully agree with making accounts as secure as possible (I have for years been advising everyone I know into the habit of making them not only complex, but nothing related to them, and changing passwords regularly), As with cars, the more secure, the less likely there will be a problem.
Several years ago I ran a experiment in a complex containing 18 different companies, With their approval, I tried to hack into their accounts and was successful with over half of them (10) within minutes, due to poor or no security (namely not changing the wifi passwords from factory settings), and I managed further intrusion on 6 out of the 10 due to poor passwords (2 actually used "password" and one used the company name to make it easy for the staff). They were shocked and amazed how easy it was and a major wake up call for them to improve their security.
Legally, these people are criminals and should be treated as such!!!
Gary
January 24, 2016PS :- when I say "these people" in the last paragraph, I mean the HACKERS are CRIMINALS., ALL BECAUSE THEY ARE INTERFERING WITH SOMEONE ELSE'S PROPERTY WITHOUT PERMISSION.
So obvious that even a small child understands that concept!!!
jt
February 24, 2016If I keep my social security card in a box at a kisok at the local mall, protected with a 4 digit pin that is all 1s (1111), whose fault is it when my social security card goes missing? Am I really going to blame the person that guessed the first option? Or should I maybe have picked a better code. People are naturally curious, and are going to try things to see if they work, regardless of intent.
My analogy really hinges on your understanding of what it means to have something be "someone else's property". If I keep my hypothetical box in my basement, where only I would have natural access to it, is that different than me keeping the box at my local mall where thousands of people walk by it every day? Is where I keep my property important in maintaining that it is in fact "my property"? If I put it in a location where other people share that space to keep their own boxes, does that change the situation at all with whose responsibility it becomes when the contents of that box is revealed due to an insecure lock?
Honestly I don't disagree with you at all that the criminals are the hackers and that what they are doing is bad. your analogy of your locked car inside your locked garage however doesn't quite hold up the same because when you put your information online you are inherently putting it in an insecure space where the entire world has access to it. It's more like you keep your locked car with a bunch of stuff inside of it in an unsupervised parking lot in the middle of downtown Detroit. Now we get to the fun bit, where your password is the equivalent to your car key. You use a car key right? Because locking it with a big button that says "Open Sesame!" would be stupid right?
Basically this list is a good one because it really is intended to tell people to stop using big "Open Sesame!" buttons to secure their personal property, when they decide they want to keep that personal property in a place where anyone could easily get to it.
Finally, just because you decided to shout at people and over-simplify the matter, instead of taking personal responsibility for the dumb decision to make your password the word "password", go ask a child if they know the difference in keeping their favorite toy in their bedroom vs leaving it at the park, and get back to me on how obvious it is when you don't keep hold of your "personal property". also remember, possession is 9/10ths of the law, so if it isn't in your house, it isn't yours.
KIM
August 12, 2016To JT - Actually you are incorrect. It is like leaving your car parked on the street or public garage with packages in the back. You can lock it or not, but if someone wants in they are going to get in, it is just how easy do you want to make it for them. Car alarm on, doors locked, windows cracked, or wrapped in duct tape - your choice.
It doesn't really matter because ultimately, if a person breaks into the car - however easy you make it - it is the person's that broke in the cars fault.
Yeah, the person that left it parked in a public place with stuff in it wasn't too bright, especially if they didn't use additional safety measures, but it is their property and not the person that broke into it.
Just because there are immoral people out there who can't understand the basic primary school moral of don't touch other people's stuff, doesn't put the blame on the individual who is the victim in the scenario. It may make them stupid or human but not exactly their fault from a legal perspective.
That is unless they are taping the key to the front window with a sign - here take me.... then yes, completely their fault.
Greg
February 3, 2016wrong. regular people's account passwords are not "hacked" on a regular basis, and password rules have got out of control, forcing users to keep a log somewhere of all their passwords (or to get software to handle all their thousands of passwords). it's pretty ridiculous that someone needs to create an 8 digit mixed password with upper and lower case letters and special characters to add and/or check points on a baby diaper site. REALLY?!? Is some mastermind criminal going to steal my huggies account from me and tell the world how many diapers I buy a week?
Passwords are phished, not hacked, and it is usually the user's fault by not following simple rules like "don't follow links in e-mail" or don't respond to pop-ups on the web that say "your computer is infected, quick! push this button", etc.
I do agree that the people setting up these phish sites should be prosecuted harshly if they can be found, but there should really be a single point contact like "911" on a phone that people can report suspicious websites or e-mails so they can be shut down, and then they should be shut down immediately.
SC
March 30, 2016Calm down bud.
Gert
January 20, 2016If I had to devellop a new algorithm to generate passwords just trying to get into an account your list would come in very handy as a first attempt, before generating combinations of letters, numbers and punctuations.
thedicemaster
January 21, 2016any hacker that plans on ever using brute force to hack into an account will already have a list like this containing thousands of passwords.
many would rather ask a million people for their password, and would get a few thousand replies
Jens Lange
January 20, 2016There is a fail in the ranking-podium-graphic: On the 2nd podium is not "12345678", it is "password"
Morgan
January 20, 2016Thanks, good catch!
Helmut
January 26, 2016There is a second error in that "1234567890" was listed in 2014 as "#6 (Unchanged)". http://www.secureidnews.com/news-item/25-worst-passwords-of-2014/
sagar ganatra
January 20, 2016really Nice List Liked It
Thanks
Sagar Ganatra
David
January 20, 2016Awesome!
ნიკუშა
January 20, 20164. Qwerty its my password for facebook ! ))
Darkshait
January 20, 20161 How many people out of the 2 milllion have the 123456 as passsword?
2 what % of the 2 million have are using one of those 25 most used password?
Morgan
January 20, 20161) About 1% 2) About 3%
Spooner
January 20, 2016Does that include the government, who does that type of thing regularly as a matter of course? (And no, not just against foreign powers)
https://www.eff.org/deeplinks/2016/01/eff-pries-more-transparency-zero-days-governments-grasp
Michael
January 20, 2016Just fyi, the podium graphic should have "password" on the #2 podium. Still, love the article every year!
Morgan
January 20, 2016Yes, good catch!
Ed Krumpston
January 20, 2016@SysOps,
Can you please remove my luggage password from this list? Current list compromises my security. Thanks.
Morgan
January 20, 2016+1 for any Spaceballs reference :)
Ken Kreager
January 20, 2016As a computer professional I've been using 8 character/nummber/special character passwords for more than twenty years. Never been hacked. I hate websites that won't allow the use of special characters.
canal pirate
April 23, 2016I agree that special characters should be allowed. That would help to mix up the various combinations needed for distinct passwords.
crooch
January 20, 2016Very enlightening
Brian
January 20, 2016What if the government stepped in enabling an authority to issue two-factor authentication via USB thumbdrives? Set a standard. Let's move on past this problem.
Helmut
January 26, 2016Whenever the "government" steps in, civil libertarians and conspiracy theorists lament that Big Brother is watching - not always unreasonably,.
Bengt
January 21, 2016How many of these accounts are just scratch accounts people create to get by some arbitrary limitation (for example, you might need to have a Facebook account to sign up for something else) and so people just don't care about the password?
Frank
January 21, 2016What I don't get is how hackers are allowed to have a billion goes at guessing a password. When I fail five times I get locked out. Why don't they?
Geoff
February 23, 2016I used to wonder at that as well...I'm guessing that the hackers copy the encrypted password file from a database that they hack. Once it's on their CPU they can hack as long as they want.
Andy
January 21, 2016Is there a more extensive list available for download anywhere? Like top 100, or 1000? Or one that includes the percentage of users that use each password?
Sincerely, definitely not a hacker harvesting passwords. :)
Morgan
January 21, 2016Hi Andy, you should take a look at Xato's release of 10,000 passwords -- great data set there
Thumrong
January 24, 2016Is "password" at Rank # 1 and # 24 the same? I think these simple passwords may be used in a group. The people in the group don't care much about security.
Rodney
January 29, 2016In #24, the "oh" is a zero.
Eldora
April 15, 2016I can already tell that's gonna be super heplufl.
Inno
February 1, 2016Well said, but why not promote 2fa and mfa in this same publication. I suppose it can help defeat the basic password hacks.
Kilian Metcalf
February 10, 2016Any advice on how to remember these bizarro 12-character passwords that are meaningless strings? I currently have 84 sites that I use frequently, all password protected. Since I'm not supposed to use the same password for more than one site, and I'm not supposed to have easily remembered passwords, and I'm not supposed to write them down, then ??? Right now I have them all in a Word file called Read Me. I know no one ever looks at a Read Me file, so even if I'm hacked, I figure they're safe.
Morgan
February 11, 2016Well, actually that's what this site and service are all about. Give TeamsID a try. I think you'll like it :)
China
April 15, 2016At last some raiianoltty in our little debate.
Den
August 31, 2016You can generate a password like "nA5Uma!!T5X#Va8u, D3ECeze#UtHac2Sa, 5ukE3+ph3truFEGa" using any online password generator and then just write down it on the desk, stiker or in the text file mypasswords.txt on the desktop or onedrive. Then when you enter a password on the facebook you input your changed password using your own modification formula.
Sample formula 1: 5th letter increased three times (you shouldn't note or tell your formula, keep it in your mind)
You passwords to access: "nA5Upa!!T5X#Va8u, D3ECjze#UtHac2Sa, 5ukE6+ph3truFEGa"
Sample formula 2: add my favorite day at the begin and month at the end of password (you shouldn't note or tell your formula, keep it in your mind)
You passwords to access: "31thnA5Uma!!T5X#Va8uAug, 31thD3ECeze#UtHac2SaAug, 31th5ukE3+ph3truFEGaAug"
Sample formula 3: reverse 4 letters at the beginning and at the end (you shouldn't note or tell your formula, keep it in your mind)
You passwords to access: "U5Anma!!T5X#u8aV, CE3Deze#UtHaaS2c, Eku53+ph3truaGEF"
Weakness: it can be kept in the db as open format and then can be compared with your passwords from the text file to find your formula.
P.S. You can use one your formula for all your passwords, but you shouldn't tell about it with anyone.
Den
August 31, 2016Also you can use website name where you login in for your formula to make passwords different for each service. E'g. add the last and the first letter of the sitename after the fifth letter (facebook: nA5Umkfa!!T5X#Va8u, twitter: D3ECertze#UtHac2Sa, instagram: 5ukE3mi+ph3truFEGa).
Den
August 31, 2016The best formula is when new symbols appear in your open password, otherwise hackers can use dictionary from your password which is maximum of number of your password length. So the password "abc" changed to "cba" contains the same three letters and it's very easy to verify all variations "abc, bca, cab, ..." (6 variations). But if your formula adds some new symbols then it needs to verify all letters, symbols, numbers or punctuation.
Leo Martinez
September 16, 2016Hi! I am creating an infographic for a project in school about passwords. I wanted to include the top ten most common passwords and also a Bar Chart using the amount of people who are using the top ten ( Individually ) For example : 123456 - 200,564 people , password - 155,546 people, etc. Is there a way you could provide this information?